Dell Technologies has stepped up its game with a powerful suite of data protection tools designed to shield businesses from breaches, ransomware, and data loss.
Here’s how Dell’s solutions can be your frontline defense—and what makes them stand out in today’s crowded cybersecurity market.
1. Proactive Defense with Intelligent Threat Detection
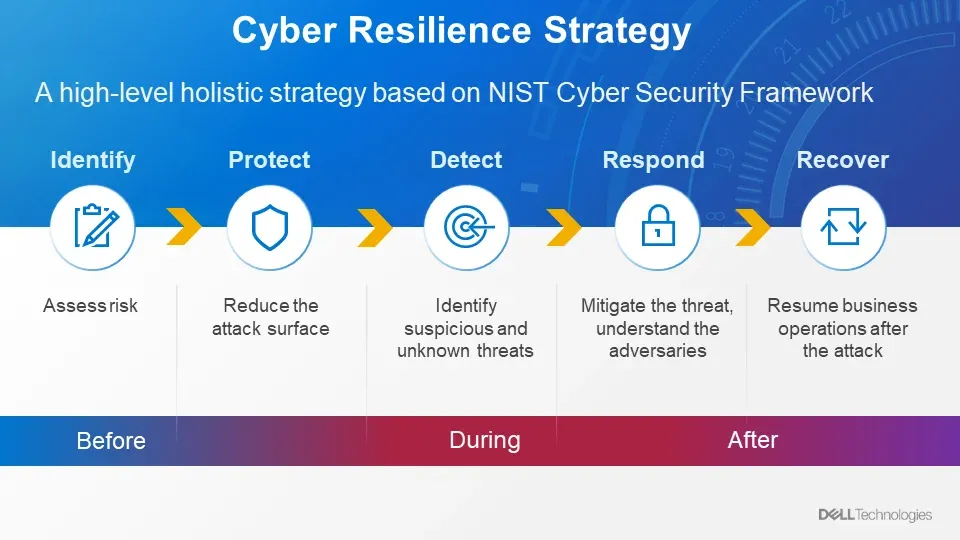
Dell’s new data protection tools are built on AI-driven analytics that constantly monitor for unusual behavior across your infrastructure.
Rather than relying solely on perimeter-based defense, Dell employs advanced anomaly detection to flag threats before they cause damage.
This real-time monitoring helps IT teams detect suspicious activities, such as unauthorized access or rapid data encryption—common signs of ransomware.
Key benefit: Early detection and response significantly reduce breach impact time and data exposure.
2. Air-Gapped Backup & Recovery to Minimize Downtime
Even with top-tier defense, no system is invincible.
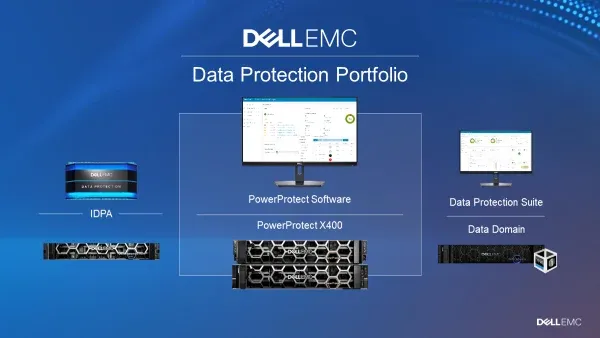
Dell's integrated backup and disaster recovery solution, PowerProtect, ensures that your data is always recoverable—even in the event of a full-scale breach or encryption attack.
The system utilizes immutable, air-gapped backups—copies of your data that cannot be altered or deleted by attackers.
Key benefit: Fast, secure recovery minimizes downtime and gets your business back on track without paying ransoms.
3. Security Management for Scalable Protection
One of Dell’s biggest advantages is its seamless, centralized management console.
IT administrators can monitor, configure, and manage data protection policies across physical, virtual, and cloud environments—all from a single dashboard.
This simplifies compliance, audit preparation, and real-time response.
Key benefit: Saves time, ensures consistency, and enables scalable security across hybrid and multi-cloud environments.
Final Thought
Dell’s approach to data protection combines intelligence, automation, and resilience.
Whether you're a small business or a global enterprise, these tools offer a critical layer of defense in a threat landscape where every second—and every byte—counts.
If you're dealing with (or worried about) a breach, Dell’s solutions could be the difference between a quick recovery and a costly catastrophe.